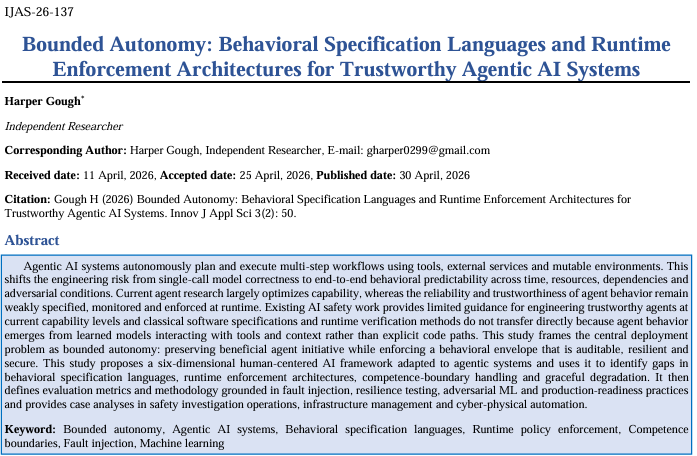
Bounded Autonomy: Behavioral Specification Languages and Runtime Enforcement Architectures for Trustworthy Agentic AI Systems
Keywords:
- Bounded autonomy,
- Agentic AI systems,
- Behavioral specification languages,
- Runtime policy enforcement,
- Competence boundaries,
- Fault injection,
- Machine learning
Abstract
Agentic AI systems autonomously plan and execute multi-step workflows using tools, external services and mutable environments. This shifts the engineering risk from single-call model correctness to end-to-end behavioral predictability across time, resources, dependencies and adversarial conditions. Current agent research largely optimizes capability, whereas the reliability and trustworthiness of agent behavior remain weakly specified, monitored and enforced at runtime. Existing AI safety work provides limited guidance for engineering trustworthy agents at current capability levels and classical software specifications and runtime verification methods do not transfer directly because agent behavior emerges from learned models interacting with tools and context rather than explicit code paths. This study frames the central deployment problem as bounded autonomy: preserving beneficial agent initiative while enforcing a behavioral envelope that is auditable, resilient and secure. This study proposes a six-dimensional human-centered AI framework adapted to agentic systems and uses it to identify gaps in behavioral specification languages, runtime enforcement architectures, competence-boundary handling and graceful degradation. It then defines evaluation metrics and methodology grounded in fault injection, resilience testing, adversarial ML and production-readiness practices and provides case analyses in safety investigation operations, infrastructure management and cyber-physical automation.
Downloads
References
1. Adepoju S (2023) Cascading failure modes in model-as-a-service architectures: When your dependencies think. International Journal of Scientific Research in Civil Engineering 7(6): 109-120.
2. Xi Z, Chen W, Guo X, He W, Ding Y, et al. (2023) The rise and potential of large language model-based agents: A survey. arXiv preprint.
3. Wang L, Ma C, Feng X, Zhang Z, Yang H, et al. (2024) A survey on large language model based autonomous agents. Frontiers of Computer Science 18(6) 186345.
4. Paleyes A, Urma RG, Lawrence ND (2022) Challenges in deploying machine learning: A survey of case studies. ACM Computing Surveys 55(6): 1-29.
5. Notaro P, Cardoso J, Gerndt M (2021) A survey of AIOps methods for failure management. ACM Transactions on Intelligent Systems and Technology 12(6): 1-45.
6. Cheng P, Xu Z, Wang Z, Zhao Y, Li T, et al. (2024) A survey on failure analysis and fault injection in AI Systems. ACM Transactions on Software Engineering and Methodology 35(1): 1-42.
7. Kharchenko V, Illiashenko O, Morozova O, Sokolov S (2023) Resilience and resilient systems of artificial intelligence: Taxonomy, models and methods. Algorithms 16(3): 165.
8. Kumar A, Goyal N (2017) Survey on resilient machine learning. arXiv preprint.
9. Breck E, Cai S, Nielsen E, Salib M, Sculley D (2017) The ML test score: A rubric for ML production readiness and technical debt reduction. In Proc IEEE Big Data 1123-1132.
10. Huang L, Joseph AD, Nelson B, Rubinstein BIP, Tygar JD (2011) Adversarial machine learning. In Proc. 4th ACM Workshop on Security and Artificial Intelligence 43-58.
11. Rose S, Borchert O, Mitchell S, Connelly S (2020) Zero trust architecture. NIST Special Publication 800-207.
12. Adepoju SA, Adepoju MA (2026) From portals to case graphs: A reference architecture and benchmark for safety investigation operations with agentic orchestration. Journal of Information Systems Engineering and Management 11(1) 1-15.
13. Adepoju SA (2025) How machine learning can revolutionize building comfort: Accessing the impact of occupancy prediction models on HVAC control system. World Journal of Advanced Research and Reviews 25(1) 2315-2327.
14. Adepoju S, David S (2025) An intelligent API framework for real-time occupancy-based HVAC integration in smart building management systems. Journal of Knowledge Learning and Science Technology 4(1): 61-70.
15. Adepoju S (2024) Deep learning for smart water grids: A targeted review of leak detection technologies. International Journal of Scientific Research in Computer Science, Engineering and Information Technology 10(1) 344-355.
16. Papernot N, McDaniel P, Sinha A, Wellman MP (2018) SoK: Security and privacy in machine learning. In Proc. IEEE European Symposium on Security and Privacy (EuroS&P) 399-414.
17. Saria S, Subbaswamy A (2019) Tutorial: Safe and reliable machine learning. arXiv preprint.
18. Adepoju S, Adepoju M (2025) Cognitive biases: Understanding and designing fair AI systems for software development. Journal of Knowledge Learning and Science Technology 4(2) 44-54.
19. Adepoju S (2023) Github copilot’s impact on developer productivity: A review of early evidence. International Journal of Scientific Research in Science and Technology 10(4) 814-822.
20. Adepoju MAO, Adepoju SA (2025) Mapping the evolution: IT roles and skills requirements in the age of AI. World Journal of Advanced Research and Reviews 25(2): 1-11.